General Discussion
Related: Editorials & Other Articles, Issue Forums, Alliance Forums, Region ForumsPresident's 'rat out your co-worker' plan, unlikely to work experts say
ugh. this makes my gorge rise.
In an initiative aimed at rooting out future leakers and other security violators, President Barack Obama has ordered federal employees to report suspicious actions of their colleagues based on behavioral profiling techniques that are not scientifically proven to work, according to experts and government documents.
The techniques are a key pillar of the Insider Threat Program, an unprecedented government-wide crackdown under which millions of federal bureaucrats and contractors must watch out for “high-risk persons or behaviors” among co-workers. Those who fail to report them could face penalties, including criminal charges.
Obama mandated the program in an October 2011 executive order after Army Pfc. Bradley Manning downloaded hundreds of thousands of documents from a classified computer network and gave them to WikiLeaks, the anti-government secrecy group. The order covers virtually every federal department and agency, including the Peace Corps, the Department of Education and others not directly involved in national security.
Under the program, which is being implemented with little public attention, security investigations can be launched when government employees showing “indicators of insider threat behavior” are reported by co-workers, according to previously undisclosed administration documents obtained by McClatchy. Investigations also can be triggered when “suspicious user behavior” is detected by computer network monitoring and reported to “insider threat personnel.”
Read more here: http://www.mcclatchydc.com/2013/07/09/196211/linchpin-for-obamas-plan-to-predict.html#storylink=cpy
East Coast Pirate
(775 posts)you should have nothing to hide.
FreakinDJ
(17,644 posts)Cronus Protagonist
(15,574 posts)McCarthy.
burnodo
(2,017 posts)I thought this was a 2-party country with two parties fundamentally different from each other.
Demo_Chris
(6,234 posts)Sorry, that's just how it is. It the imaginations of some Bush represents the ultimate evil, and always somewhere further down the road that we happen to be currently. But that's just a fantasy. Obama has taken the programs that Bush and Clinton started, and he has taken them to a place that aught to leave even the most die-hard fantatic party loyalist positively cringing in horror.
And he's our guy -- only he's not and never has been.
In any case, Bush (as despicable as he was) didn't claim the power to murder Americans, at will, any time and any place, with no congressional oversight, no judicial process, no limits but his own secret unaccountable judgement. That's the kind of power reserved for Kings and tyrants. Nor did Bush claim the authority to spy on every single American, and to database their private information and communications in open defiance of the Constitution. So let's leave off with the "almost like Bush" nonsense -- it serves no purpose but to minimize what we are dealing with today.
truebluegreen
(9,033 posts)Enthusiast
(50,983 posts)markiv
(1,489 posts)always rolling forward, always getting bigger and worse
Demo_Chris
(6,234 posts)Not the government employee rushing in to help, or inspect, or to build a bridge, but the government servant in mask and jackboots, sometimes waving a flag, other times a cross, but always carrying a gun.
Response to cali (Original post)
LumosMaxima This message was self-deleted by its author.
HooptieWagon
(17,064 posts)...people they simply don't like and can't get along with, etc. The govt will be spending all their time evaluating frivolous complaints...like DU Jury system on steroids.
frylock
(34,825 posts)because you can bet someone will make a report just to fuck with someone.
Cronus Protagonist
(15,574 posts)Really.
Savannahmann
(3,891 posts)The program was launched in 2011, and Snowden acted almost two years later. So two years of people watching co-workers out of the corner of their eyes, did nothing, other than teach people to practice their poker faces.
President Obama would have been better served looking over the secrets, and seeing which ones he could justify if they were ever found out. We would have been better served if we had launched a new Moral Governance model, in which the rights of the people were the first and foremost goal on the minds of Government workers, instead of trying to catch the man/woman who was thinking of exposing the immoral and illegal.
Fumesucker
(45,851 posts)Very little of this shit is a surprise to the security services of other nations, most secret clearance stuff is designed to keep the public from finding out.
The public is the real enemy.
Chemisse
(30,817 posts)All of this drama is to keep things hidden from the American public.
GoneFishin
(5,217 posts)And, anything embarrassing or unethical can be cloaked in secrecy.
Fumesucker
(45,851 posts)Of course Romney's win would be the fault of those who are the furthest politically from Romney and would be least likely to vote for him because shut up, that's why.
But at least everyone would loathe government spying, they are wearing me down, I'm really tired of having to argue against government spying with supposed liberals/progressives.
I thought liberals wanted to help their fellow men, not spy on them.
Le Taz Hot
(22,271 posts)"Of course Romney's win would be the fault of those who are the furthest politically from Romney and would be least likely to vote for him because shut up, that's why."
I just snorted coffee. ![]()
![]()
GoneFishin
(5,217 posts)Art_from_Ark
(27,247 posts)If Romney had won, there would be a whole lot different atmosphere around here.
ctsnowman
(1,903 posts)a lot of the most ardent defenders are conservative Democrats and they are probably happy with the right leaning things that Obama does for that reason. As a commie lib myself I find half what Obama does way too far to the right for me.
RC
(25,592 posts)It is those that claim to be Democrats. Read their posts subjectively, as they try to fit conservative views into a Left leaning mind-set. "What government spying, there is no government spying. It's all Snowden's fault for exposing our spying to the enemy."
leftstreet
(36,112 posts)Demo_Chris
(6,234 posts)Capt. Obvious
(9,002 posts)Fumesucker
(45,851 posts)Hint; not Obama.
winter is coming
(11,785 posts)Enthusiast
(50,983 posts)Skittles
(153,193 posts)they would not make these excuses for just any Dem
Egalitarian Thug
(12,448 posts)The geezers and those god damned kids can be the force we need to overcome the jackass pseudo-liberals.
woo me with science
(32,139 posts)forestpath
(3,102 posts)coworkers you rat out for nothing? Or testing employees with fakery and prosecuting the ones who don't jump at the bait?
Maybe Obama thinks morale isn't low enough already!
Chef Eric
(1,024 posts)War is Peace.
Freedom is Slavery.
Ignorance is Strength.
Chemisse
(30,817 posts)Sure we don't have screens in our homes with watching eyes. The government is more insidious than that. Instead they gaze at our homes with infrared and satellites and 'listen' to our communications with electronic monitoring.
RitchieRich
(292 posts)on my mobile, laptop, and on my desktop PC. Any mid level hacker could access the hardware and turn it on. Standard on most new devices. (regarding "Sure we don't have screens in our homes with watching eyes)
Chemisse
(30,817 posts)nadinbrzezinski
(154,021 posts)New TVs have forward facing cameras
Waiting For Everyman
(9,385 posts)Apparently empathy or giving a damn is now defined as a security risk.
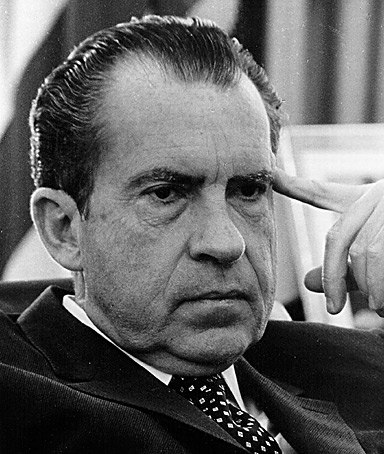
Obama is going off the Nixon deep end. And this Stasi-esque lunacy will probably still be in place long after he leaves office.
cali
(114,904 posts)It makes me so damn sad- among other things.
leftyohiolib
(5,917 posts)bemildred
(90,061 posts)It's never "Maybe we are not doing this right?"
It's always "How can we make them do what we want?"
democrank
(11,103 posts)The Government could use some of those portable tin classrooms we no longer need from all the public schools that have been closed down and place them here and there all around the country. Turn them into little manufacturing sheds and pump out Made in the U.S.A. wearable spyware. Offer the spywear at slightly above cost to any corporations that contributed over a certain amount to The Party and presto!......millions of workers with wristwatch cameras, cameras attached to their eyeglasses, cameras taped to their Starbucks cups, cameras on their shirt buttons. Maybe we could even bring back billboards with photos of some Supreme Court members saying, "Cameras Are People, Too!" Some government Spy Expert could design and send out a helpful bulk-mailing manual which might save the troubled United States Postal Service!
I`m really excited about this. Folks would be put back to work and at the same time, help their government flush out all the people with suspicious behavior. It would sort of be like that spaghetti thing we keep hearing about.....throw enough of it against the wall and something is bound to stick.
cali
(114,904 posts)BornLooser
(106 posts)Would never abuse this "program" for self advancement, retaliation, ego boosting, and of course political payback. This will be a huge clusterfuck, and perhaps that's by design? If I can see the trees from the forest, they GOTTA know where this will lead...
Chemisse
(30,817 posts)Not only are employees being spied on, but they are also forced to be spies.
kelliekat44
(7,759 posts)see my post below. People here are making those who care about protecting Federal resources and processes seem like criminals or gangsters who "rat" on wrongdoers.
struggle4progress
(118,338 posts)the Responsible Sharing and Safeguarding of Classified Information
http://www.whitehouse.gov/the-press-office/2011/10/07/executive-order-13587-structural-reforms-improve-security-classified-net
http://www.whitehouse.gov/briefing-room/presidential-actions/executive-orders
Section 1. Policy. Our Nation's security requires classified information to be shared immediately with authorized users around the world but also requires sophisticated and vigilant means to ensure it is shared securely. Computer networks have individual and common vulnerabilities that require coordinated decisions on risk management.
This order directs structural reforms to ensure responsible sharing and safeguarding of classified information on computer networks that shall be consistent with appropriate protections for privacy and civil liberties. Agencies bear the primary responsibility for meeting these twin goals. These structural reforms will ensure coordinated interagency development and reliable implementation of policies and minimum standards regarding information security, personnel security, and systems security; address both internal and external security threats and vulnerabilities; and provide policies and minimum standards for sharing classified information both within and outside the Federal Government. These policies and minimum standards will address all agencies that operate or access classified computer networks, all users of classified computer networks (including contractors and others who operate or access classified computer networks controlled by the Federal Government), and all classified information on those networks.
Sec. 2. General Responsibilities of Agencies.
Sec. 2.1. The heads of agencies that operate or access classified computer networks shall have responsibility for appropriately sharing and safeguarding classified information on computer networks. As part of this responsibility, they shall:
(a) designate a senior official to be charged with overseeing classified information sharing and safeguarding efforts for the agency;
(b) implement an insider threat detection and prevention program consistent with guidance and standards developed by the Insider Threat Task Force established in section 6 of this order;
(c) perform self-assessments of compliance with policies and standards issued pursuant to sections 3.3, 5.2, and 6.3 of this order, as well as other applicable policies and standards, the results of which shall be reported annually to the Senior Information Sharing and Safeguarding Steering Committee established in section 3 of this order;
(d) provide information and access, as warranted and consistent with law and section 7(d) of this order, to enable independent assessments by the Executive Agent for Safeguarding Classified Information on Computer Networks and the Insider Threat Task Force of compliance with relevant established policies and standards; and
(e) detail or assign staff as appropriate and necessary to the Classified Information Sharing and Safeguarding Office and the Insider Threat Task Force on an ongoing basis.
Sec. 3. Senior Information Sharing and Safeguarding Steering Committee.
Sec. 3.1. There is established a Senior Information Sharing and Safeguarding Steering Committee (Steering Committee) to exercise overall responsibility and ensure senior-level accountability for the coordinated interagency development and implementation of policies and standards regarding the sharing and safeguarding of classified information on computer networks.
Sec. 3.2. The Steering Committee shall be co-chaired by senior representatives of the Office of Management and Budget and the National Security Staff. Members of the committee shall be officers of the United States as designated by the heads of the Departments of State, Defense, Justice, Energy, and Homeland Security, the Office of the Director of National Intelligence, the Central Intelligence Agency, and the Information Security Oversight Office within the National Archives and Records Administration (ISOO), as well as such additional agencies as the co-chairs of the Steering Committee may designate.
Sec. 3.3. The responsibilities of the Steering Committee shall include:
(a) establishing Government-wide classified information sharing and safeguarding goals and annually reviewing executive branch successes and shortcomings in achieving those goals;
(b) preparing within 90 days of the date of this order and at least annually thereafter, a report for the President assessing the executive branch's successes and shortcomings in sharing and safeguarding classified information on computer networks and discussing potential future vulnerabilities;
(c) developing program and budget recommendations to achieve Government-wide classified information sharing and safeguarding goals;
(d) coordinating the interagency development and implementation of priorities, policies, and standards for sharing and safeguarding classified information on computer networks;
(e) recommending overarching policies, when appropriate, for promulgation by the Office of Management and Budget or the ISOO;
(f) coordinating efforts by agencies, the Executive Agent, and the Task Force to assess compliance with established policies and standards and recommending corrective actions needed to ensure compliance;
(g) providing overall mission guidance for the Program Manager-Information Sharing Environment (PM-ISE) with respect to the functions to be performed by the Classified Information Sharing and Safeguarding Office established in section 4 of this order; and
(h) referring policy and compliance issues that cannot be resolved by the Steering Committee to the Deputies Committee of the National Security Council in accordance with Presidential Policy Directive/PPD-1 of February 13, 2009 (Organization of the National Security Council System).
Sec. 4. Classified Information Sharing and Safeguarding Office.
Sec. 4.1. There shall be established a Classified Information Sharing and Safeguarding Office (CISSO) within and subordinate to the office of the PM-ISE to provide expert, fulltime, sustained focus on responsible sharing and safeguarding of classified information on computer networks. Staff of the CISSO shall include detailees, as needed and appropriate, from agencies represented on the Steering Committee.
Sec. 4.2. The responsibilities of CISSO shall include:
(a) providing staff support for the Steering Committee;
(b) advising the Executive Agent for Safeguarding Classified Information on Computer Networks and the Insider Threat Task Force on the development of an effective program to monitor compliance with established policies and standards needed to achieve classified information sharing and safeguarding goals; and
(c) consulting with the Departments of State, Defense, and Homeland Security, the ISOO, the Office of the Director of National Intelligence, and others, as appropriate, to ensure consistency with policies and standards under Executive Order 13526 of December 29, 2009, Executive Order 12829 of January 6, 1993, as amended, Executive Order 13549 of August 18, 2010, and Executive Order 13556 of November 4, 2010.
Sec. 5. Executive Agent for Safeguarding Classified Information on Computer Networks.
Sec. 5.1. The Secretary of Defense and the Director, National Security Agency, shall jointly act as the Executive Agent for Safeguarding Classified Information on Computer Networks (the "Executive Agent"
Sec. 5.2. The Executive Agent's responsibilities, in addition to those specified by NSD-42, shall include the following:
(a) developing effective technical safeguarding policies and standards in coordination with the Committee on National Security Systems (CNSS), as re-designated by Executive Orders 13286 of February 28, 2003, and 13231 of October 16, 2001, that address the safeguarding of classified information within national security systems, as well as the safeguarding of national security systems themselves;
(b) referring to the Steering Committee for resolution any unresolved issues delaying the Executive Agent's timely development and issuance of technical policies and standards;
(c) reporting at least annually to the Steering Committee on the work of CNSS, including recommendations for any changes needed to improve the timeliness and effectiveness of that work; and
(d) conducting independent assessments of agency compliance with established safeguarding policies and standards, and reporting the results of such assessments to the Steering Committee.
Sec. 6. Insider Threat Task Force.
Sec. 6.1. There is established an interagency Insider Threat Task Force that shall develop a Government-wide program (insider threat program) for deterring, detecting, and mitigating insider threats, including the safeguarding of classified information from exploitation, compromise, or other unauthorized disclosure, taking into account risk levels, as well as the distinct needs, missions, and systems of individual agencies. This program shall include development of policies, objectives, and priorities for establishing and integrating security, counterintelligence, user audits and monitoring, and other safeguarding capabilities and practices within agencies.
Sec. 6.2. The Task Force shall be co-chaired by the Attorney General and the Director of National Intelligence, or their designees. Membership on the Task Force shall be composed of officers of the United States from, and designated by the heads of, the Departments of State, Defense, Justice, Energy, and Homeland Security, the Office of the Director of National Intelligence, the Central Intelligence Agency, and the ISOO, as well as such additional agencies as the co-chairs of the Task Force may designate. It shall be staffed by personnel from the Federal Bureau of Investigation and the Office of the National Counterintelligence Executive (ONCIX), and other agencies, as determined by the co-chairs for their respective agencies and to the extent permitted by law. Such personnel must be officers or full-time or permanent part-time employees of the United States. To the extent permitted by law, ONCIX shall provide an appropriate work site and administrative support for the Task Force.
Sec. 6.3. The Task Force's responsibilities shall include the following:
(a) developing, in coordination with the Executive Agent, a Government-wide policy for the deterrence, detection, and mitigation of insider threats, which shall be submitted to the Steering Committee for appropriate review;
(b) in coordination with appropriate agencies, developing minimum standards and guidance for implementation of the insider threat program's Government-wide policy and, within 1 year of the date of this order, issuing those minimum standards and guidance, which shall be binding on the executive branch;
(c) if sufficient appropriations or authorizations are obtained, continuing in coordination with appropriate agencies after 1 year from the date of this order to add to or modify those minimum standards and guidance, as appropriate;
(d) if sufficient appropriations or authorizations are not obtained, recommending for promulgation by the Office of Management and Budget or the ISOO any additional or modified minimum standards and guidance developed more than 1 year after the date of this order;
(e) referring to the Steering Committee for resolution any unresolved issues delaying the timely development and issuance of minimum standards;
(f) conducting, in accordance with procedures to be developed by the Task Force, independent assessments of the adequacy of agency programs to implement established policies and minimum standards, and reporting the results of such assessments to the Steering Committee;
(g) providing assistance to agencies, as requested, including through the dissemination of best practices; and
(h) providing analysis of new and continuing insider threat challenges facing the United States Government.
Sec. 7. General Provisions. (a) For the purposes of this order, the word "agencies" shall have the meaning set forth in section 6.1(b) of Executive Order 13526 of December 29, 2009.
(b) Nothing in this order shall be construed to change the requirements of Executive Orders 12333 of December 4, 1981, 12829 of January 6, 1993, 12968 of August 2, 1995, 13388 of October 25, 2005, 13467 of June 30, 2008, 13526 of December 29, 2009, 13549 of August 18, 2010, and their successor orders and directives.
(c) Nothing in this order shall be construed to supersede or change the authorities of the Secretary of Energy or the Nuclear Regulatory Commission under the Atomic Energy Act of 1954, as amended; the Secretary of Defense under Executive Order 12829, as amended; the Secretary of Homeland Security under Executive Order 13549; the Secretary of State under title 22, United States Code, and the Omnibus Diplomatic Security and Antiterrorism Act of 1986; the Director of ISOO under Executive Orders 13526 and 12829, as amended; the PM-ISE under Executive Order 13388 or the Intelligence Reform and Terrorism Prevention Act of 2004, as amended; the Director, Central Intelligence Agency under NSD-42 and Executive Order 13286, as amended; the National Counterintelligence Executive, under the Counterintelligence Enhancement Act of 2002; or the Director of National Intelligence under the National Security Act of 1947, as amended, the Intelligence Reform and Terrorism Prevention Act of 2004, as amended, NSD-42, and Executive Orders 12333, as amended, 12968, as amended, 13286, as amended, 13467, and 13526.
(d) Nothing in this order shall authorize the Steering Committee, CISSO, CNSS, or the Task Force to examine the facilities or systems of other agencies, without advance consultation with the head of such agency, nor to collect information for any purpose not provided herein.
(e) The entities created and the activities directed by this order shall not seek to deter, detect, or mitigate disclosures of information by Government employees or contractors that are lawful under and protected by the Intelligence Community Whistleblower Protection Act of 1998, Whistleblower Protection Act of 1989, Inspector General Act of 1978, or similar statutes, regulations, or policies.
(f) With respect to the Intelligence Community, the Director of National Intelligence, after consultation with the heads of affected agencies, may issue such policy directives and guidance as the Director of National Intelligence deems necessary to implement this order.
(g) Nothing in this order shall be construed to impair or otherwise affect:
(1) the authority granted by law to an agency, or the head thereof; or
(2) the functions of the Director of the Office of Management and Budget relating to budgetary, administrative, or legislative proposals
(h) This order shall be implemented consistent with applicable law and appropriate protections for privacy and civil liberties, and subject to the availability of appropriations.
(i) This order is not intended to, and does not, create any right or benefit, substantive or procedural, enforceable at law or in equity by any party against the United States, its departments, agencies, or entities, its officers, employees, or agents, or .any other person.
BARACK OBAMA
THE WHITE HOUSE,
October 7, 2011
struggle4progress
(118,338 posts)cali
(114,904 posts)and what's with posting the impenetrable regs?
struggle4progress
(118,338 posts)what concerns you most there
cali
(114,904 posts)I've already pointed out what concerns me: policy that encourages government employees to report "suspicious" behavior. do you deny that's the policy?
struggle4progress
(118,338 posts)cali
(114,904 posts)Why don't YOU address it, since it's so important to you and tell me what you agree with?
(h) providing analysis of new and continuing insider threat challenges facing the United States Government.
Sec. 7. General Provisions. (a) For the purposes of this order, the word "agencies" shall have the meaning set forth in section 6.1(b) of Executive Order 13526 of December 29, 2009.
(b) Nothing in this order shall be construed to change the requirements of Executive Orders 12333 of December 4, 1981, 12829 of January 6, 1993, 12968 of August 2, 1995, 13388 of October 25, 2005, 13467 of June 30, 2008, 13526 of December 29, 2009, 13549 of August 18, 2010, and their successor orders and directives.
(c) Nothing in this order shall be construed to supersede or change the authorities of the Secretary of Energy or the Nuclear Regulatory Commission under the Atomic Energy Act of 1954, as amended; the Secretary of Defense under Executive Order 12829, as amended; the Secretary of Homeland Security under Executive Order 13549; the Secretary of State under title 22, United States Code, and the Omnibus Diplomatic Security and Antiterrorism Act of 1986; the Director of ISOO under Executive Orders 13526 and 12829, as amended; the PM-ISE under Executive Order 13388 or the Intelligence Reform and Terrorism Prevention Act of 2004, as amended; the Director, Central Intelligence Agency under NSD-42 and Executive Order 13286, as amended; the National Counterintelligence Executive, under the Counterintelligence Enhancement Act of 2002; or the Director of National Intelligence under the National Security Act of 1947, as amended, the Intelligence Reform and Terrorism Prevention Act of 2004, as amended, NSD-42, and Executive Orders 12333, as amended, 12968, as amended, 13286, as amended, 13467, and 13526.
(d) Nothing in this order shall authorize the Steering Committee, CISSO, CNSS, or the Task Force to examine the facilities or systems of other agencies, without advance consultation with the head of such agency, nor to collect information for any purpose not provided herein.
Divernan
(15,480 posts)Sec. 6.1. There is established an interagency Insider Threat Task Force that shall develop a Government-wide program (insider threat program) for deterring, detecting, and mitigating insider threats, including the safeguarding of classified information from exploitation, compromise, or other unauthorized disclosure, taking into account risk levels, as well as the distinct needs, missions, and systems of individual agencies. This program shall include development of policies, objectives, and priorities for establishing and integrating security, counterintelligence, user audits and monitoring, and other safeguarding capabilities and practices within agencies.
There you have vague, undefined and totally unrestricted language allowing subjective interpretation and application by & within each federal agency.
One of the principles of legislative drafting - which I have done for a legislature, and which I taught law students how to do - is that a key section of a law is the "definitions" section, which controls how the law can be interpreted and implemented. How important is a definition of a word? Just ask sharp lawyer, Bill Clinton: "It depends on what your definition of 'is' is." The phrase "other safeguarding capabilities and practices" could not be vaguer or more open-ended. With a phrase like this tacked on, there are NO limits on the type and degree of spying on employees which can be done. I think most employees understand they have no expectation of privacy at work re their computer, their desk, etc. Put this order can be interpreted to authorize spying on them 24/7. Put a tracking device on their personal car? Follow them on their lunch break? Track their credit card usage? It's all good under this order.
The scenario envisioned by this Order sounds like an unbelievable dystopia.
struggle4progress
(118,338 posts)or nullified by Executive Order. And there are plenty of Federal records which almost anyone will agree should not be released to the public: personal income tax returns are a prime example. The Manning and Snowden cases have shown that some records normally regarded as restricted can be captured and released by individuals
BTW the current state of the law on vehicular tracking devices seems to be given by a SCOTUS ruling last January:
Supreme Court rules warrant needed for GPS tracking
By Joan Biskupic, USA TODAY Updated 1/24/2012 1:33 AM
... Monday's decision specifically applies when police install a GPS tracking device on a person's car, but five justices suggested in concurring statements that a warrant might similarly be needed for prolonged surveillance through smartphones or other devices with GPS capabilities. The Global Positioning System, originally developed for the military, relies on satellites that transmit to receivers that calculate the latitude and longitude of a location. A GPS device installed by police can be used to follow a person 24 hours a day. Data can be collected and analyzed far more efficiently and economically than if a team of agents followed a person. The court reversed the cocaine-trafficking conviction of a Washington, D.C., nightclub owner. In 2005, police attached a GPS device to a Jeep owned by Antoine Jones while it was parked in a public lot. Agents then used evidence of Jones' travels over four weeks to help win the conviction on conspiracy to distribute cocaine ...
http://usatoday30.usatoday.com/news/washington/judicial/story/2012-01-23/supreme-court-GPS/52754354/1
cali
(114,904 posts)and predictably you ducked a response to it.
Divernan
(15,480 posts)ex·ec·u·tive or·der
Noun
A rule or order issued by the president to an executive branch of the government and having the force of law.
And the principles of judicial interpretation of the language of said order, should any victims of this Executive Order end up defending themselves in court, would be EXACTLY as I described in my post. Of course that makes the optimistic assumption that any federal employees "detained" under authority of this Order would ever see the light of day in a public court.
And your bald claim "existing statues aren't modified"?!?!?! There is a vast universe of existing "statutes", local, state and federal out there. How amazing that you are so omniscient that you can make such a proclamation. Here's a clue for your consideration: There's a whole field of study and practice called "Conflict of Laws." And while you're looking that up, take a gander at the concept of habeas corpus - just for old times sake.
Even your weak attempt to distract from the discussion at hand fails. The case you cited is not remotely applicable or binding as it refers to police surveillance of a cocaine trafficker. Furthermore "suggestions" in concurring opinions are not "the current state of the law." Such "suggestions" are only dicta, and in this case, not even relevant to the OP and discussion in this thread. The case you mentioned in no manner addresses issues of oh, scary, "national security!" or secret warrants approved by faceless unelected judges in a rubber stamp court. And may I point out, that while appointments to federal court judgeships must receive legislative approval, there are no such approvals required for the secret court relied upon by the feds to churn out warrants on demand.
If you are incapable of responding to a question, or a challenge, why don't you admit it, instead of making up what you would like the law to be.
And I suggest you go to law school before you attempt to interpret Supreme Court opinions!
davidn3600
(6,342 posts)Never thought we'd see this kind of practice in America.
kelliekat44
(7,759 posts)any form if they witness it. This is not new and dedicated civil servants have been doing just that for years. I believe it formally started under RR as the GOP and the RWingers became fanatical haters of the government for using tax dollars to help people. Only problem was that too many reports were coming in about contractors who were taking jobs under the "contracting out" movement began under RR. However, for years scientists were turning in other scientists for fudging research data and other scientific misconduct. The public paid little or no attention to the many civil servants that uncovered fraud and abuse. The media paid no attention until the $600 military toilet was unveiled back in the late 70s early 80s. Most people back then appreciated honesty and integrity of civil servants trying to protect the resources and creditability of using taxpayer dollars to help, not harm the country. People even received rewards and awards for doing so. All of a sudden it's a bad and evil idea?
Volaris
(10,274 posts)1) If Bush had done this, we would be screaming our bloody heads off..Just saying.
2) "If you have nothing to hide, you have nothing to fear." works both ways: If the PUBLIC Government isn't into anything dirty, and is willing to act as a fair and honest broker bewteen other Nations on the world stage, their internal State Department e-mails shouldn't have any dirt in them, ANYWAY NOW SHOULD THEY???? You want us to stay the hell out of your e-mail, then you can damn-well DO THE SAME.
3) Ummmm... by the time we finished Jr. High most of us learned that, as a general rule, being a rat was a pretty effective way to get yourself hit in the head. I know at that level it's not National Security or anything, but...yeah....
(oh and by the way if Bush had done this, we would be screaming our bloody heads off..just sayin')
This isn't about National Security. It's about the Image Security of National figures. And in this country, that image isn't important enough for the rest of us to turn rat-bastard snitch on each other. That's some KGB-level nastiness right there....
ctsnowman
(1,903 posts)N2doc (sp?) posted a week or so ago. "if you see someone say something" ![]()
bullwinkle428
(20,630 posts)"GODWIN!!1!1!", so I'll just leave it at that for now.
Apophis
(1,407 posts)avaistheone1
(14,626 posts)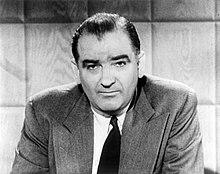
boilerbabe
(2,214 posts)Blue_In_AK
(46,436 posts)We were talking about it here weeks ago.
Harmony Blue
(3,978 posts)American public opinion has shifted about the NSA spy programs and secret FISA courts that the corporate media has found it profitable now to start talking about such topics.
winter is coming
(11,785 posts)So, there's a leaker under every bed, and failing to report them could land you in trouble.
1) Is this still the USA?
2) If the government is that concerned about the existence of numerous would-be leakers, WTF is it doing that it fears people would feel compelled to leak about? And, if the government knows it's doing something that objectionable/wrong, why are they still doing it?
mick063
(2,424 posts)when we can toss Godwin's law out the window?
truebluegreen
(9,033 posts)kenny blankenship
(15,689 posts)HipChick
(25,485 posts)I saw these notifications circulating in 2011..I don't recall any outrage back then...
great white snark
(2,646 posts)Didn't he do something horrible when he was 2? Peed in a pool or something? I'm OUTRAGED!
cali
(114,904 posts)you want to cheer this, go right ahead, i think it should be condemned. And its hardly my fault that I'm just hearing about it. From the article:
Under the program, which is being implemented with little public attention, security investigations can be launched when government employees showing “indicators of insider threat behavior” are reported by co-workers, according to previously undisclosed administration documents obtained by McClatchy. Investigations also can be triggered when “suspicious user behavior” is detected by computer network monitoring and reported to “insider threat personnel.”
Read more here: http://www.mcclatchydc.com/2013/07/09/196211/linchpin-for-obamas-plan-to-predict.html#storylink=cpy
cali
(114,904 posts)HipChick
(25,485 posts)let me see if I can find the thread
steve2470
(37,457 posts)2- not necessary.
1- This needs no explanation, many posters have already explained it.
2- I think that MOST, not all, federal employees have enough patriotism/nationalism/love of country in them that they will automatically report genuinely suspicious things to the authorities. I would, IF...IF..IF...it was genuine. Otherwise, I would discard the thought and go on with my business. Turning someone in is extremely serious and not to be done lightly.
Yes, there will always be a very very small minority of government employees who wish to do harm to the USA in some way, but this program is not needed, to me. If someone can prove to me that my second point is not true, I will consider a rational alternative.
AllINeedIsCoffee
(772 posts)That this might not work.
woo me with science
(32,139 posts)This America is turning into something I don't recognize and that is very frightening to me.
Savannahmann
(3,891 posts)I found this gem late last night. I was tied up, too busy to do much posting. But I thought that it was interesting.
http://www.dailymail.co.uk/news/article-2359673/Obama-executive-order-requires-federal-government-employees-learn-spy-workers-prevent-WikiLeaks-type-disclosures.html
The link is following the development of this story. A quote from it is telling.
He told McClatchy that the answer to spotting potential leakers shouldn't be 'to have a Stasi-like response,' referring to the feared East German communists' secret police.
OK, so it's just fine and fucking dandy to spy on everyone in the world. It's perfectly fine, no problem with Civil Rights to collect all the data of every person in the nation, and then use half a dozen different programs to take the data and sort it and then fold, spindle, and mutilate it. We have to protect the nation. But when the Watchers start watching each other? Oh that's a true problem there. That could create a repressive kind of culture.
How obviously hypocritical do you have to be? How nutty is this argument. Why is it OK for them to do the watching, but not to suffer the watching? But we have the answer to one question. Who watches the watchers? Nobody, and is the way the watchers want it.
Somebody let me know when we can start to roll this crap back, because from where I sit, it looks like this might be our last chance.