MAJOR OPENSSL BUG 'PUTS LARGE NUMBERS OF WEBSITES AT RISK' (Heartbleed Bug)
Source: CBR
As many as two-thirds of websites currently online could be affected by security flaw.
A serious vulnerability has been discovered in the open-source encryption software used in many of the world's websites that could allow attackers to steal a variety of information unnoticed.
The 'Heartbleed' bug potentially allows access to the memory of systems that currently run one of several vulnerable versions of the OpenSSL cryptographic software library.
OpenSSL is used to protect websites, instant messaging, email server protocols, virtual private networks and other online communications.
The flaw could reveal the authentication and encryption keys used to protect traffic, as well as details such as usernames and passwords.
Due to the nature of the of the bug, however, the attackers will leave no trace in server logs, so there is no way of knowing if the flaw has been exploited.
Read more: http://www.cbronline.com/news/security/major-openssl-bug-puts-large-numbers-of-websites-at-risk-4210975
Change your passwords.
Orrex
(63,220 posts)Don't tell!
stevenleser
(32,886 posts)The next time you logon to a website that hasn't implemented fixes will put your new password at risk, right?
2naSalit
(86,765 posts)to be the case.
Paulie
(8,462 posts)So if you check the security certificate and it is new as of 4/8/2014 then you're good to go on changing that site's password. Changing it before they update both parts means you'll need to change it again.
Not all sites use OpenSSL but a majority do.
2naSalit
(86,765 posts)somewhat vindicated for not conducting transactions online that require any financial info or personal stuff that could be used in ID theft.
But I have been changing passwords anyway.
![]()
LiberalArkie
(15,728 posts)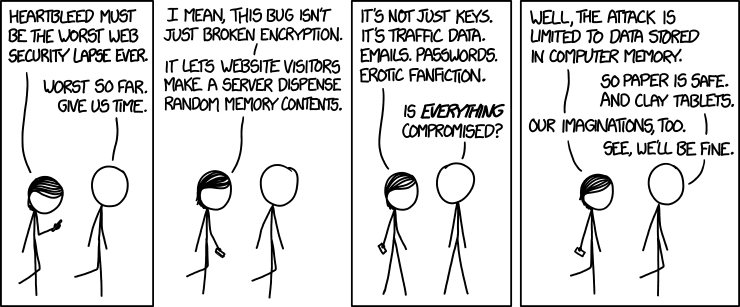
L0oniX
(31,493 posts)KurtNYC
(14,549 posts)but only reveals upto 64K in random chunks.
http://it.slashdot.org/story/14/04/07/2354258/openssl-bug-allows-attackers-to-read-memory-in-64k-chunks
randome
(34,845 posts)
[hr][font color="blue"][center]If you don't give yourself the same benefit of a doubt you'd give anyone else, you're cheating someone.[/center][/font][hr]
Paulie
(8,462 posts)64k of is about 32,000 ASCII characters. And there is no limit how many times you can ask for a chunk of 64k.
What's worse is it also can be part of the servers SSL private key. Spend 5 minutes and you will have massive amounts of accounts and potentially data to impersonate as the server!
Pretty bad bug.
TrogL
(32,822 posts)I checked all my stuff and it's earlier.
dickthegrouch
(3,183 posts)Just because all your software is based on more than 4 year-old technology and therefore is not susceptible to this bug, does NOT mean your site is not just as easily compromised in some other way.
Get it updated, soon.
TrogL
(32,822 posts)blkmusclmachine
(16,149 posts)marions ghost
(19,841 posts)why they didn't do something about this sooner. I'm just a lowly user and not real tech savvy, but it seems to me SOMEbody knew about this and it was inconvenient to reveal it widely.
I'm suspicious.